With cyber-attacks increasing in volume and sophistication, our IT and cyber security consulting services keep your business safe and secure.
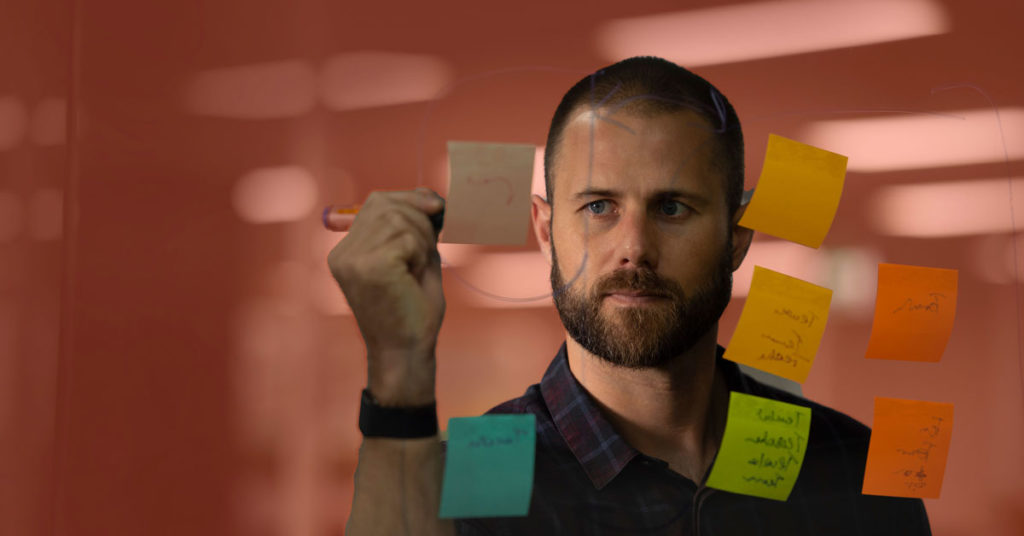
There’s no room for complacency around information security management systems. With so many potential entry points to your business – from compromised cloud applications and file sharing applications to everyday texts and emails – the scope for potential attack is ubiquitous.
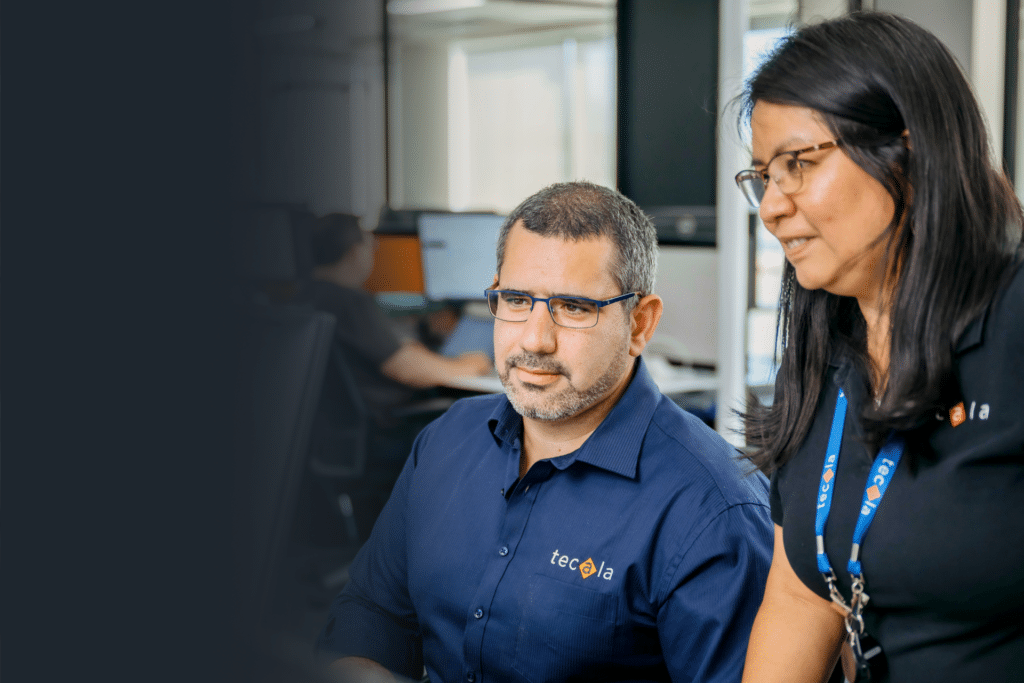
The good news is that through being ICT security specialists and cyber security solution providers in Australia, Tecala have you covered. By way of a fully integrated Cyber and ICT Security Services portfolio, Tecala is able to hunt, investigate, and stop threats before they become business disrupting events.
This includes our ability to accurately assess your cyber security threat landscape and exposure to attack, as well as implementing a multi-faceted approach to managing your information security management systems.
Built on a combination of cutting-edge XDR technology and leading-edge threat intelligence, our Managed Detection Response (MDR) Service optimises your security approach to stop breaches and minimise business risk.
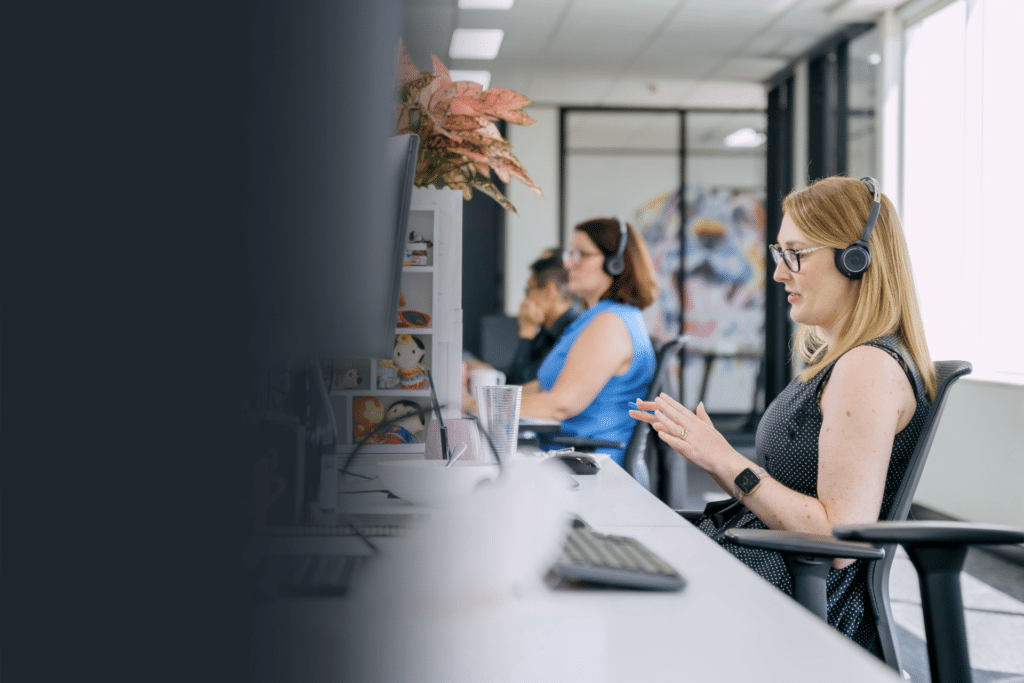
Through our Consultancy and Advisory Services teams, we ensure your employees have the awareness, training, and ongoing support they need to be risk aware and responsible.
When all these IT security services are delivered to you through our award-winning Managed Security Services team, we can dramatically reduce your risk of attack and its potential impact on your data, your business, and your reputation.
No-one wants to be tomorrow’s headline for a targeted intrusion or opportunistic attack. With our thorough IT and cyber security consulting services, we’ll ensure around-the-clock threat protection that’s proactive and tailored to your business in your unique threat landscape.